Graylog has always been associated with log management, metrics, SIEM and security monitoring—but it’s also a great tool for creative, low-cost experiments in a home
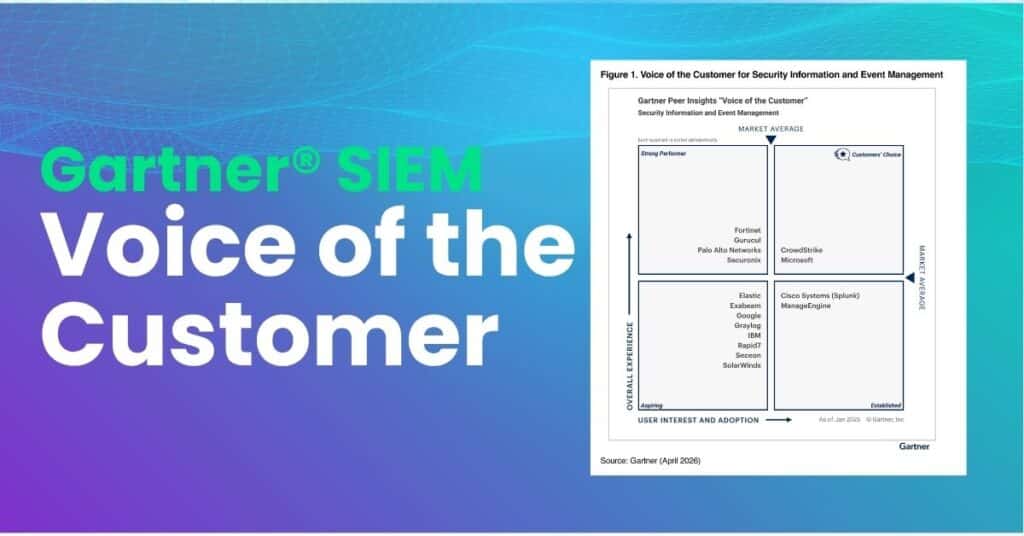
Key Points Graylog received an overall rating of 4.6 out of 5.0 in the 2026 Gartner® Peer Insights SIEM Voice of the Customer report 86%*

When people start driving, one of the first things they learn is how to set the rear-view and side-view mirrors. Whether driving locally or on