Graylog has always been associated with log management, metrics, SIEM and security monitoring—but it’s also a great tool for creative, low-cost experiments in a home lab. I wanted to use
Graylog has always been associated with log management, metrics, SIEM and security monitoring—but it’s also a great tool for creative, low-cost experiments in a home lab. I wanted to use
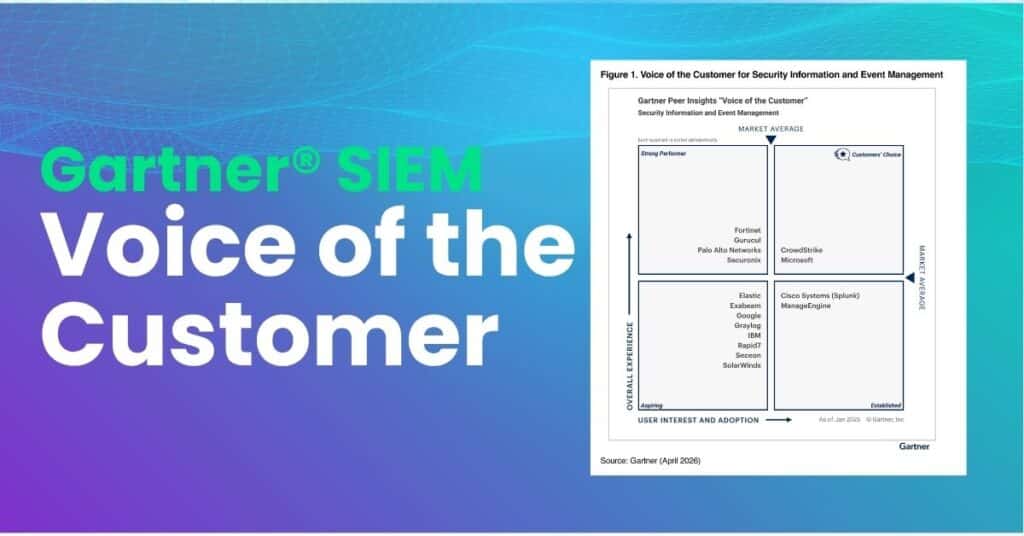
Key Points Graylog received an overall rating of 4.6 out of 5.0 in the 2026 Gartner® Peer Insights SIEM Voice of the Customer report 86%* of verified enterprise reviewers said

When people start driving, one of the first things they learn is how to set the rear-view and side-view mirrors. Whether driving locally or on the highway, these mirror configurations

What to Expect? Graylog 7.1 is built for lean security and IT operations teams who need real outcomes, not more tools, more add-ons, or more manual work. This 30-minute deep
Like most organizations, your company likely invested in various Microsoft products. The Microsoft ecosystem provides businesses with nearly every kind of technology necessary, from workstation operating systems to Azure to

In 2023, India’s Parliament approved and published The Digital Personal Data Protection Act (DPDPA). In many ways, the DPDPA is similar to other regulations, like the General Data Protection Regulation

The Essential Eight identifies the most critical cybersecurity risk mitigation controls, providing a set of minimum baseline strategies. As organizations work to mature the security posture, the Essential Eight maturity

Published by the Open Worldwide Application Security Project (OWASP) in 2025, the OWASP Top 10 for Agentic Applications 2026 identifies security risks that organizations need to consider when implementing agentic

A long time ago, in a SOC far, far away…analysts were drowning in alerts, chasing context across fragmented screens, and watching real threats slip past detection gaps. Today, the Rebellion
In today’s data-driven world, CISOs and senior leadership need to prove that their security programs mitigate risk. Just like grades theoretically quantify how well students understand material their teachers present,
While inherently critical to today’s businesses that run on data, implementing and enforcing data security and privacy has never been straightforward. Between collecting different types of sensitive data and deploying
Free Online Graylog Analyst Training Efficient log management and analysis are crucial for maintaining robust IT infrastructures. To empower IT professionals and enthusiasts with the skills needed to harness

As a kid, fruit punch always seemed like a magical drink. A mix of orange, cherry, apple, and cranberry created a unique flavor that differed substantially from any one juice.
Subscribe to the latest in log management, security, and all things Graylog blog delivered to your inbox once a month.
Subscribe to the latest in log management, security, and all things Graylog blog delivered to your inbox once a month.
