Bringing SIEM Without Compromise to Life
Most SIEMs were built for people you don’t have and budgets you can’t afford. Graylog Security gives lean security teams full visibility, faster investigations, and smarter detection without the complexity, headcount, or cost.
Detect threats 40% faster
with high-speed search and analyst workflows
Process logs 10x faster
with a SIEM built for speed, scale and operational clarity
Close investigations faster
with automated case creation and remediation steps
Log everything. Pay only for what you use.
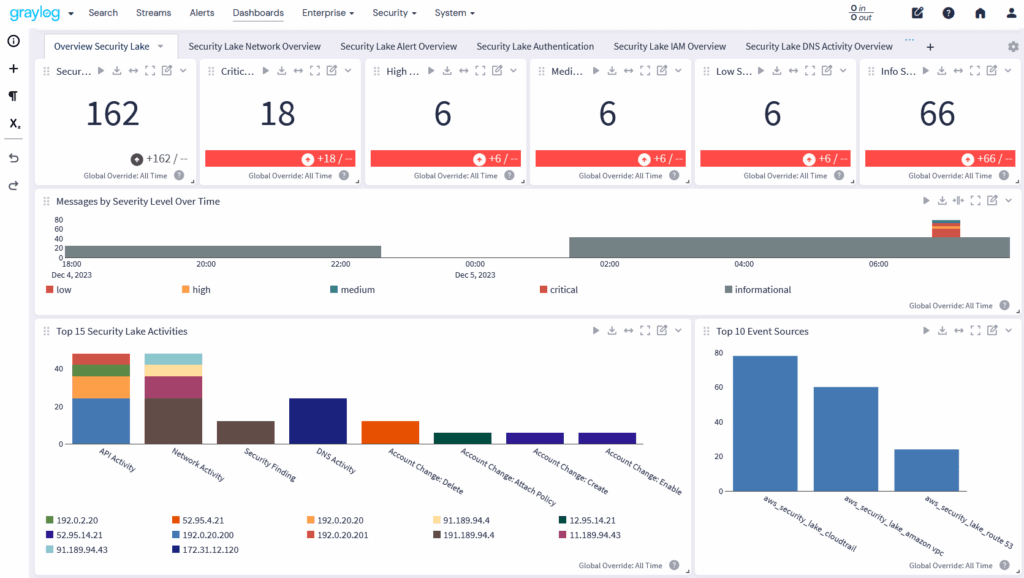
Traditional SIEMs force a choice between full visibility and affordability. Graylog Security eliminates that trade-off. Store years of logs, retrieve exactly what investigations need, and never pay for data you didn’t use.
- Built-in data lake stores years of logs affordably without counting against your license.
- See and retrieve exactly what you need, only when you need it.
- Optionally use AWS Security Lake instead with direct integration to accelerate investigations and reduce storage costs.
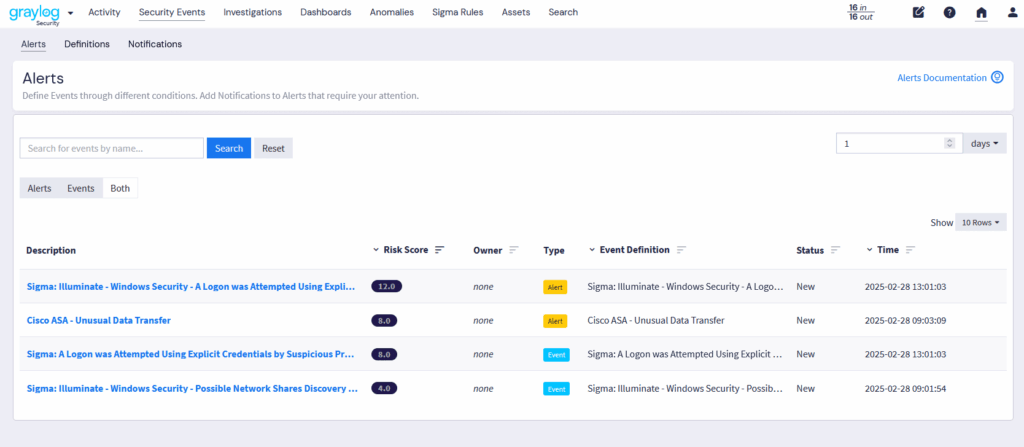
Detect what rules alone can't catch.
Most SIEMs only catch what they were explicitly built to recognize. Graylog Security’s behavioral detectors surface the attacks your rule sets miss, with full transparency into why each alert fired and the flexibility to tune it.
- Impossible Travel Detection flags credential compromise the moment a user appears in two impossible locations. No custom rules required.
- Log Volume Anomaly Detection surfaces spikes or drops that signal exfiltration or source failures before they escalate.
- Risk Score aggregation by asset matches detection sensitivity to actual organizational risk.
- Monitor the Top 10 Security Threats on day one, know where your coverage gaps are.
Close cases faster. No SOAR needed.
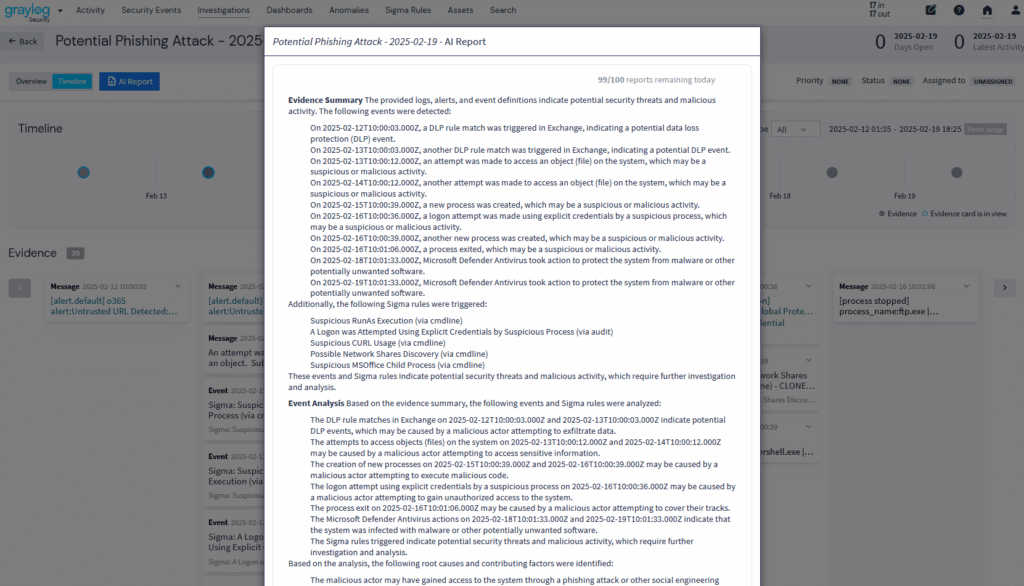
Analysts don’t have time to chase evidence across tools, rebuild timelines from scratch, or file incident reports by hand. Graylog Security automates the work that slows teams down so analysts can focus on decisions, not documentation. Every analyst works like a senior one. No SOAR needed .
- Auto-Investigation from Asset Risk Threshold builds and pre-loads the case the moment a risk score breaches your threshold. Analysts inherit a ready-to-go investigation, not a blank slate.
- Consolidated Event Procedures put every remediation step in one list. One path forward, not ten open tabs.
- Event Status Sync updates all attached evidence instantly. No drift, no rework.
- Built-in MCP server enables secure, bring-your-own LLM integration and AI Agents for advanced automation within Graylog RBAC guardrails.
- AI Investigation Summaries deliver audit-ready incident reports at case closure. Seconds, not days.
Cloud, on-prem, or hybrid. Your data, your rules.
Your environment shouldn’t dictate your security platform. Graylog Security runs cloud-native, on-premises, or hybrid with full feature parity across every deployment. Your team stays in control, your data stays where it belongs.
- Same experience across every deployment model.
- No forced SaaS limitations or compromises on data control.
- Private Sigma repo support imports detection content from GitHub, GitLab, or Bitbucket with full version control.
AI that works. Without the hype.
Security teams don’t need more AI promises. They need AI that saves time, stays explainable, and keeps analysts in charge. Graylog Security’s AI is built into the platform, not bolted on.
- Natural language queries via MCP let analysts investigate in plain English. No query language required.
- Bring your own LLM under Graylog guardrails.
- AI Investigation Summaries compile findings, timelines, and audit-ready incident reports at case closure. Analysts review and approve. Nobody writes from scratch.
- Dashboard AI assistant helps explain what’s going on and identify hidden meaning that may not be immediately obvious from the visual display
Ready to see Graylog in Action?
Built for Analysts, Trusted by Security Leaders
Security Analyst
Cut through the noise. Investigate in clicks.
Security teams are overwhelmed by false positives and alert fatigue. With Graylog Security, you’ll surface real threats faster and reduce manual work with contextual scoring and automation.
What You’ll Love:
- Threat Prioritization Engine: Entity-based risk scoring surfaces the threats that actually matter
- Context-Aware Incident Response: Investigations build themselves so analysts close cases, not paperwork
- Intuitive Analyst Experience: One-click pivots, guided search, and bulk log actions cut triage time
- AI Assistance: Summaries, guided queries, and investigation findings compiled automatically at case closure
“With Graylog Security, we focus on threats—not our SIEM.” -Senior Security Analyst, Healthcare
SIEM Admin
Take control of your SIEM—without the complexity.
Are you tired of clunky interfaces and brittle configurations? Graylog Security makes onboarding, tuning, and scaling easy with intuitive tools and intelligent automation.
What You’ll Love:
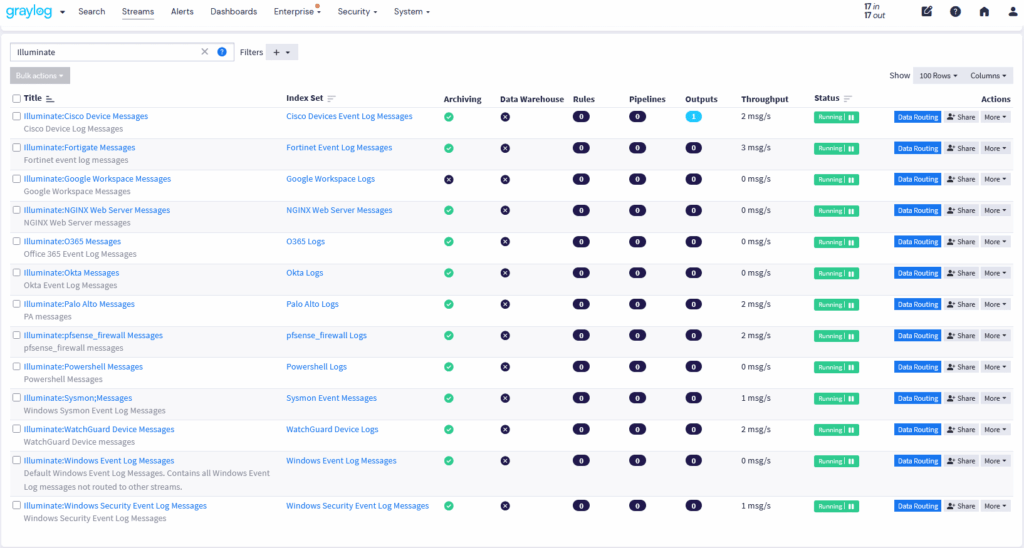
- Rapid Value Delivery: Guided onboarding and prebuilt Illuminate content activate detection from day one
- Detection Content Portability: Import Sigma rules from private GitHub, GitLab, or Bitbucket repos
- Run-Anywhere Deployment: Cloud, on-prem, or hybrid with the same capabilities and same UI
- Intelligent Data Control: Preview, tier, and retrieve data precisely without full restores or guesswork
- Attack Surface Coverage Out of the Box: Prebuilt detections and dashboards organized by attack surface eliminate coverage gaps instantly.
“We deployed Graylog in hours, not weeks—and got visibility right away.” -SIEM Admin, Public Sector
CISO
Security that scales with you—not against you.
CISOs need visibility, risk context, and control over costs. Graylog Security delivers intelligent threat detection and long-term visibility without unpredictable licensing.
What You’ll Love:
- Threat Prioritization Engine: Risk scoring per asset group with tunable thresholds your board can understand
- Detection Content Portability: Map behavioral and rule-based coverage across your full threat landscape
- Intelligent Data Control: Flexible data routing and value-based licensing put infrastructure and license costs in your hands
- AI Assistance: Audit-ready investigation summaries and incident reports generated automatically at case closure
- Coverage You Can Explain: Show what’s monitored by attack surface, where gaps remain, and how you’re closing them.
“Graylog gives us the insights we need—with budget predictability we can trust.” –CISO, Banking & Finance
MSSP
Deliver improved detection & response—at scale.
MSSPs need a platform that’s flexible, cost-efficient, and fast to operationalize across clients. Graylog Security gives you scalable, multi-tenant capabilities with automation and pricing that work.
What You’ll Love:
- Run-Anywhere Deployment: Serve multiple clients securely across cloud, on-prem, or hybrid environments
- Context-Aware Incident Response: Automated triage and consolidated procedures reduce analyst workload per client
- Intelligent Data Control: Manage per-client retention and data routing without excess cost or storage sprawl
- AI Assistance: Case documentation and handoff summaries generated automatically across every client engagement
- Consistent Coverage from Day One: Every engagement starts with standardized attack surface detections and shared triage language.
“Graylog helps us deliver premium MDR at an efficient margin.” -MSSP SOC Manager
Compliance & Audit
Audit-ready visibility without the storage sprawl.
Regulated industries rely on complete, searchable log data to prove compliance and close audits quickly. Graylog Enterprise simplifies retention and retrieval with cost-efficient storage, guided searches, and compliance-ready content packs. Parallel archive restores mean your team retrieves precisely what auditors need in hours, not weeks. Teams can meet mandates, validate findings, and respond to auditor requests instantly, without manual restores or additional staffing.
What You’ll Love:
- Intelligent Data Control: Flexible data routing and value-based licensing keep long-term retention costs under control
- Operational Resilience: Parallel archive restore retrieves precise compliance records in hours, not weeks
- Rapid Value Delivery: Prebuilt compliance content packs activate audit-ready parsing, dashboards, and alerts from day one
“Graylog Enterprise let us meet new compliance mandates with zero additional headcount. We passed our HIPAA audit in record time.” -Director of IT Compliance, Regional Healthcare Network
Graylog named in the 2025 Gartner® Magic Quadrant™ for SIEM
The SIEM Built for Teams That Can't Afford to Slow Down
Legacy SIEMs were built for 50-person 24x7 global SOCs. Yours isn't that team. Graylog Security is. Threats detected without rules. Investigations that build themselves. Audit docs that write themselves at case closure. No SOAR. No black-box AI. No surprise bills. Lean team. Full coverage. Zero compromise.