Teams encompass users, while roles indicate what the user can do/what actions they can take. Sharing at the feature/functionality level associates view, edit, and create privileges.

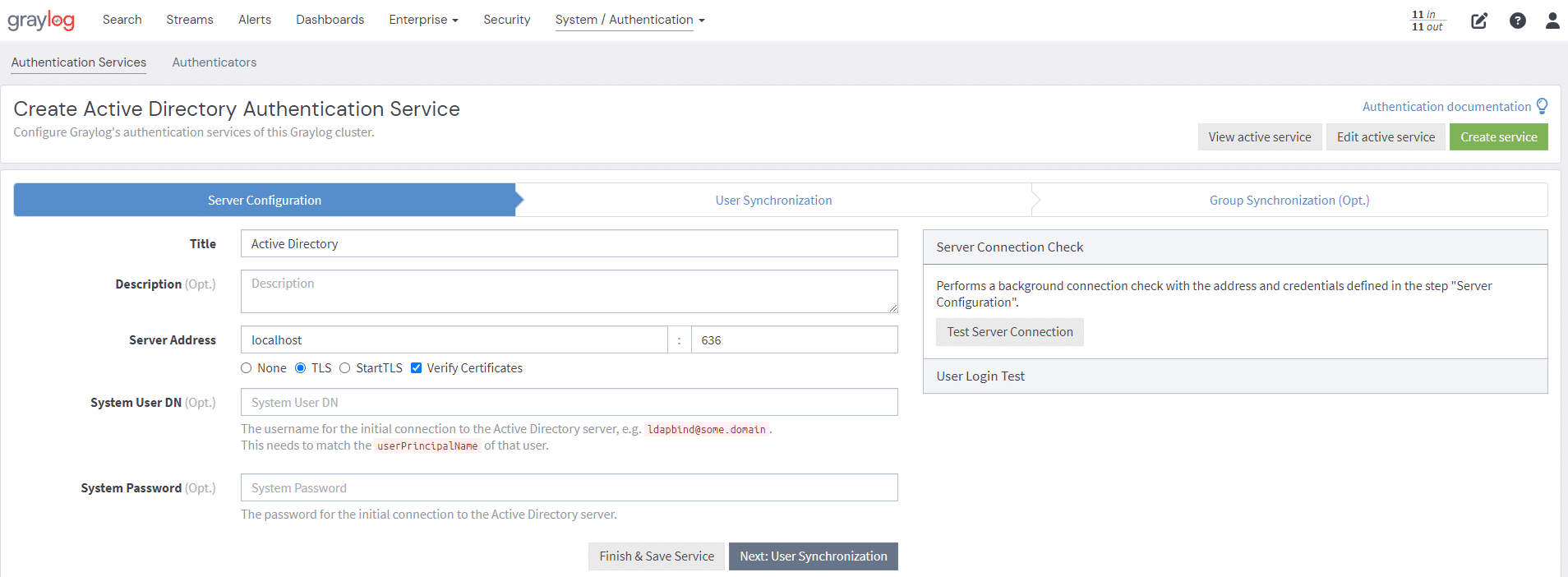
Graylog syncs with your organization’s authoritative identity source to automatically provision users with the appropriate rights and permissions to pull this all together. Graylog Enterprise maintains this synchronization when you activate the specific authentication service. Through this one-directional sharing, Graylog updates team members whenever the authoritative identity source updates for day one access upon login. Next, Graylog uses the current roles and AD groups to auto-populate access that reflects the organizational permissions structure.
You can follow a standard naming convention to make it easy to find teams using the name or a search term. For example, you can create the “Security Team,” which will make it easier to find users with similar data needs through lists of users, groups, or both. The global setting capabilities enable Admins to limit who views data more precisely, ultimately mitigating security and privacy risks. Organizations can still manually manage access and permissions if necessary.
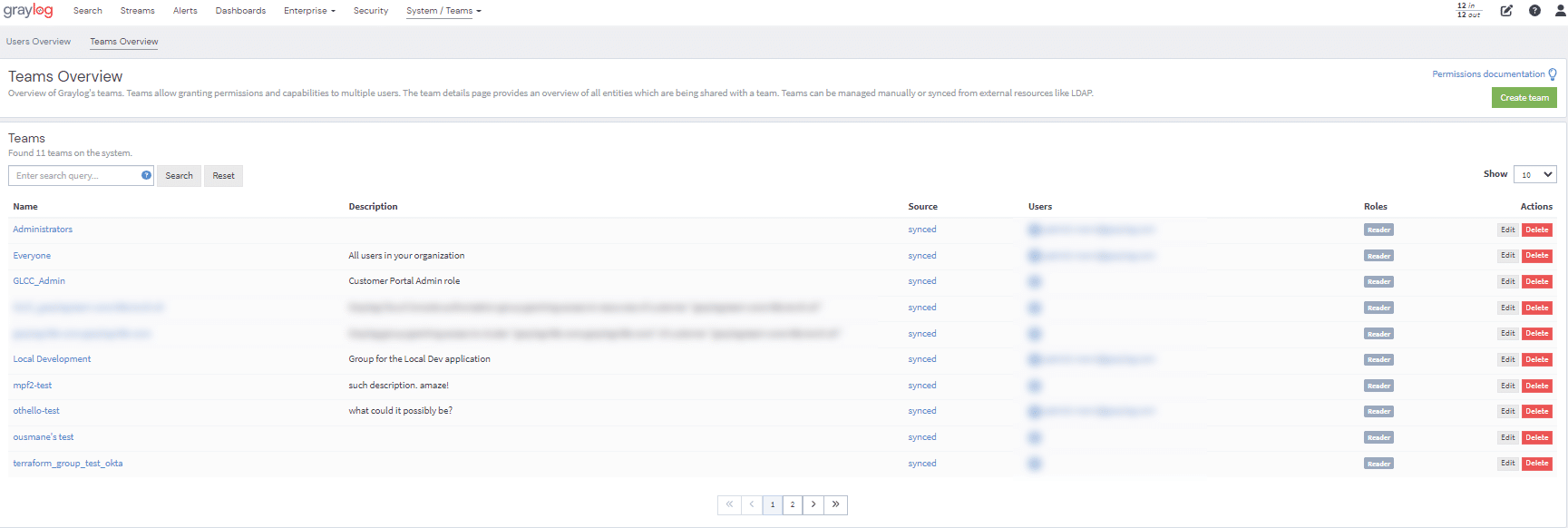
NOTE: You cannot manually manage synchronized Teams in Graylog. You have to manage them in the original identity provider. For example, if you create an LDAP team, you cannot add or remove team members in Graylog. You can (and we recommend that you do) configure the roles that accompany the team.
