As a kid, treasure hunts were fun. Someone gave you clues and a map so you could hunt down whatever hidden item they left for you. However, as a security
As a kid, treasure hunts were fun. Someone gave you clues and a map so you could hunt down whatever hidden item they left for you. However, as a security

I’m thrilled to share some incredibly exciting news – Graylog’s v6.0 is officially here! It’s been quite the journey getting to this point, filled with late nights, endless cups of
Everyone loves managed services until the bill comes in. High performance search indexers are a premium technology and have premium resource requirements. Graylog 6.0 introduces Data Tiering to put the

Graylog Has A Brand-New Look! We’re thrilled to introduce Graylog’s fresh, new look! Gone are the days of our stark, albeit eye-catching red, black, and gray. Welcome a vibrant, modern
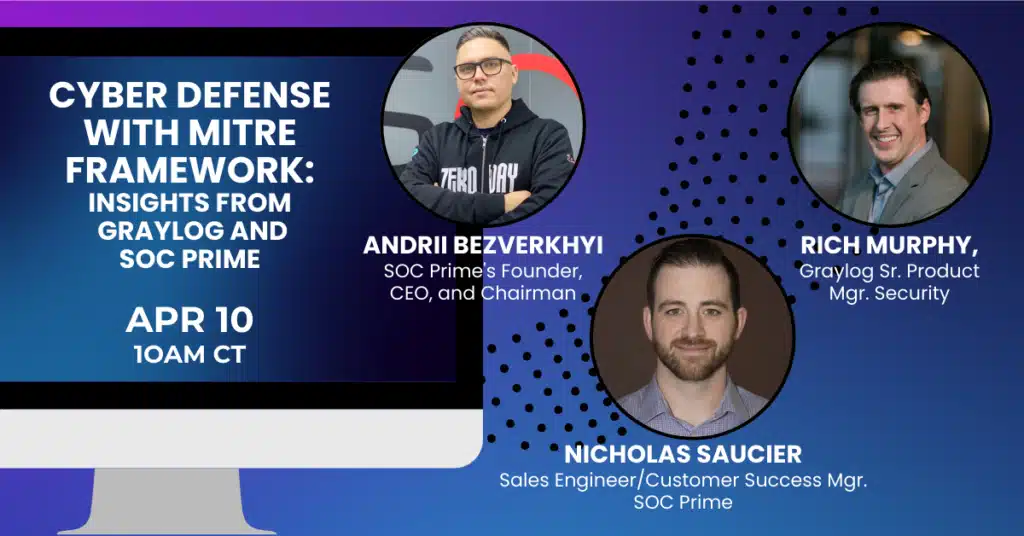
Cyber Defense with MITRE Framework: Insights from Graylog and SOC Prime In this 30-minute webinar, you will learn how to identify and neutralize threats faster using the SOC Prime
Integrations that accelerate detection and response Gartner identified security technology convergence as one of the key trends both in 2022 and 2023 as a necessity to remove complexity in the

In cybersecurity as in sports, teamwork makes the dream work. In a world where security analysts can feel constantly bombarded by threat actors, banding together to share information and strategies
In cybersecurity, “Load Balancing Graylog with Nginx: The Ultimate Guide” is your reference guide. This guide helps to install Nginx. Imagine your Graylog, already proficient at managing vast log data,

SIEM and log management provide security to your organization; these tools allow your security analysts to track events such as potential and successful breaches of your system and react accordingly.
So, you’ve done your homework. You’ve clearly defined business requirements, and you think you want to implement a Security Information and Event Management (SIEM) solution into your organization. Cloud migration

Managing configurations in a complex environment can be like playing a game of digital Jenga. Turning off one port to protect an application can undermine the service of a connected

Your senior leadership started stressing out about data breaches. It’s not that they haven’t worried before, but they’ve also started looking at the rising tide of data breach awareness. Specifically, they’re
NIST is to the US government what The Watcher is to the Marvel universe. In theory, it should simply observe the world around it, but in reality, it responds to
Products
Follow Us:
© 2024 Graylog, Inc. All rights reserved