It’s 3pm on a Wednesday, and you’re really just done with the week already. You hear that “ping” from your Slack and know that you set notifications for direct messages only, which means, ugh, you have to pay attention to this one. It’s your boss, and she’s telling you to check your email. Then you see it, the dreaded audit documentation request. This will take you the rest of today and most of tomorrow. You need to go through all your old emails, looking for the reports you sent to senior leadership. You need to look at your spreadsheets. You’re already exhausted.
If you have a centralized log management solution, reporting compliance to management might look a little bit different.
WHAT IS COMPLIANCE REPORTING?
At this point in time, almost every industry vertical and every company has some kind of compliance requirement.
For example, if you’re in hospitality, retail, e-commerce, or any other industry marketing to consumers, you probably need to comply with the following:
- European Union General Data Protection Regulation (GDPR)
- California Privacy Rights Act (CPRA) – formerly the California Consumer Privacy Act (CCPA)
If you let people pay for products or services with a credit or debit card, you need to comply with the Payment Card Industry Data Security Standard (PCI DSS).
If you’re in the healthcare industry or considered a business associate to a healthcare organization, you’ve got to manage Health Insurance Portability and Accountability Act (HIPAA) compliance.
The list goes on and on, but you get the idea.
Compliance reporting takes a few different forms:
- Documenting daily activities for continuous monitoring
- Documenting incident response, including investigation and remediation
- Providing regular reports to senior leadership
The good news is that you have the extra set of hands you need with the right centralized log management solution.
When you create dashboards, you can streamline the compliance reporting process in several ways:
- Change the date parameters for your dashboards to show activity during the requested audit period
- Create easy-to-read reports that enable management and auditors to answer their questions
- Automate your management reporting practices
REPORTING COMPLIANCE WITH CONTINUOUS MONITORING REQUIREMENTS
If you were to sit down and read through every regulation or industry standard, you’d see a lot of similarities. There’s a finite number of privacy and security control categories at a high level.
This is probably another example of the old saying, “the more things change, the more things stay the same.”
In a complex IT environment, everything changes. Remote users connect to networks from different locations and devices. Your developers might be spinning up new instances or containers. Threat actors keep changing their attack methodologies.
At the same time, you’ve got the same general control categories that help you secure data. Usually, you’re looking at:
- Access: failed logins, login successes
- Networks: firewalls, network traffic
- Endpoints: antivirus, endpoint detection and response (EDR)
- Vulnerability monitoring: vulnerability scanning, patch management
- Data: Encryption, application security
Continuous monitoring can be overwhelming if you have to do everything manually or need to look at each location separately.
SETTING ALERTS
However, with a centralized log management solution, you can create high-fidelity alerts by correlating events across these locations.
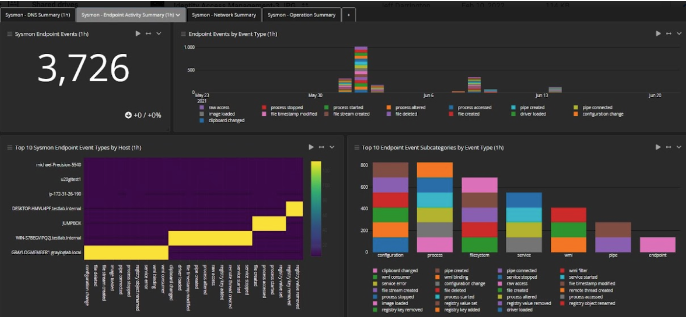
USE CASE: ENDPOINT SECURITY
Managing remote devices is hard. There’s really no other way to say it. On the other hand, one compromised device can spread a malware or ransomware infection to your entire network.
You need to know that the devices meet your security policies. Centralized log management can help you with this.
For example, you can create high fidelity alerts that aggregate and correlate log data to help you detect a potential endpoint security risk:



Using Dashboards
Sometimes, the absence of something is just as important as the existence of something.
Your alerts tell you when something abnormal happens, but you also want to show that you know what “normal” looks like. If you set up a parameterized dashboard in your centralized log management solution, you can create reports that show activity over time.
Use case: URL Filtering
Monitoring web traffic with URL filtering blocks known and unknown threats. Setting up a dashboard not only alerts you to threats, but it gives you documentation proving that nothing happened.
Once you set up your centralized log management solution, you can show that you were looking for abnormalities, and none existed. You can show that no alerts or blocks were detected by setting time constraints.
Basically, you have data that supports you were tracking the security control and that the security worked as intended because nothing abnormal triggered an alert.
It may seem boring, but it proves compliance.

Reporting Compliance with Incident Response Requirements
Let’s be honest. Security and privacy compliance mandates exist because some companies don’t do what they’re supposed to do. While continuous monitoring is the proactive requirement, incident response is the reactive requirement.
Setting high-fidelity alerts gives you the “detection” needed for a robust incident response program. However, you also have to prove that you did the following as quickly as possible:
- Investigated the alert
- Located the root cause
- Contained the threat
- Eradicated the threat
- Recovered affected systems
Compliance requirements for incident response really want to track how well companies manage their people, processes, and technologies.
Centralized log management initially existed to help IT operations teams respond to help desk calls and trace issues to keep systems running. IT Ops would start looking for the root cause of an issue by looking for abnormalities in event logs.
Basically, it’s the same process as the security incident response use case but with different outcomes.
Your leadership and auditors will want to know how quickly you were able to investigate and respond to the alert. By integrating your centralized log management solution with your ticketing system, you can prove how long it took your team to investigate an alert by tracking when the ticket was opened and closed.
Using Dashboards
Think about the process of evaluating a security incident. It’s hard to go through all the different steps needed without a little help.
You might need to review:
- User access
- User privileges
- Endpoint logs
If you have a single, easy-to-read visualization, getting to the root cause is faster, especially when talking about configuration changes that indicate an advanced persistent threat.
With the right dashboards, you can show:
- When logs documented changes: indicating the start of the event
- What types of changes they documented: what the threat actor was attempting during the incident
- When they stopped reporting the activities: showing that the threat actor is no longer acting in the system

REPORTING COMPLIANCE TO MANAGEMENT
Now we’re at the “governance” stage. Your management needs to prove that they understand risk, monitor your ability to protect systems, and engage in these reviews regularly.
They don’t actually need the deep technical issues. They need high-level, easy-to-read reports that tell them you’re doing what you’re supposed to be doing.
Guess what? The dashboards that you’re using to monitor activity can also help. You can create dashboards that show high-level metrics.
For example, you could create a dashboard showing the number of security messages:
Yes, this shows that there were logon failures, but it also shows that there were no high severity alerts. In other words, it was people who forgot their passwords, not a credential-based attack.
Once you create these dashboards, you can schedule sharing them with leadership. You and your management have an easy-to-read, automated reporting structure that meets their compliance needs.
GRAYLOG: CENTRALIZED LOG MANAGEMENT FOR REPORTING COMPLIANCE
With Graylog’s centralized log management solution, you can secure your environment and document your activities to meet compliance mandates.
Graylog makes it easy to translate your daily security activities into meaningful management reports so that your organization can prove its compliance posture. After creating dashboards, you can schedule them to be shared automatically. Meanwhile, our lightning-fast search capability and ticketing system integrations help you prove key metrics like mean time to investigate (MTTI) and mean time to respond (MTTR).