- March 22, 2023
Data’s role in business processes continues to evolve. Today, organizations collect, store, process, and transmit more personal data than ever before, and legislative bodies respond by updating privacy laws. Türkce
Data’s role in business processes continues to evolve. Today, organizations collect, store, process, and transmit more personal data than ever before, and legislative bodies respond by updating privacy laws. Türkce

In today’s digital age, the internet has become an integral part of our daily lives. From working remotely to streaming movies, we rely on the internet for almost everything. However,
As digital transformation expands the threat landscape, compliance mandates adapt to meet new challenges. In 2020, the European Commission announced its decision to accelerate its revision of the Directive on

Google Cloud Logging is an essential service for managing, analyzing, and troubleshooting logs generated from various Google Cloud services and applications. It offers a centralized platform for collecting, processing, and



İş dünyasında verilerin rolü giderek artmaktadır. Bugünlerde kurumlar geçmistekinden çok daha fazla kişisel veriyi toplamakta, saklamakta, işleme koymakta ve aktarmaktadır; buna karşın da yasal kurumlar mahremiyet yasalarını güncellemektedirler. Türkiye, 2016
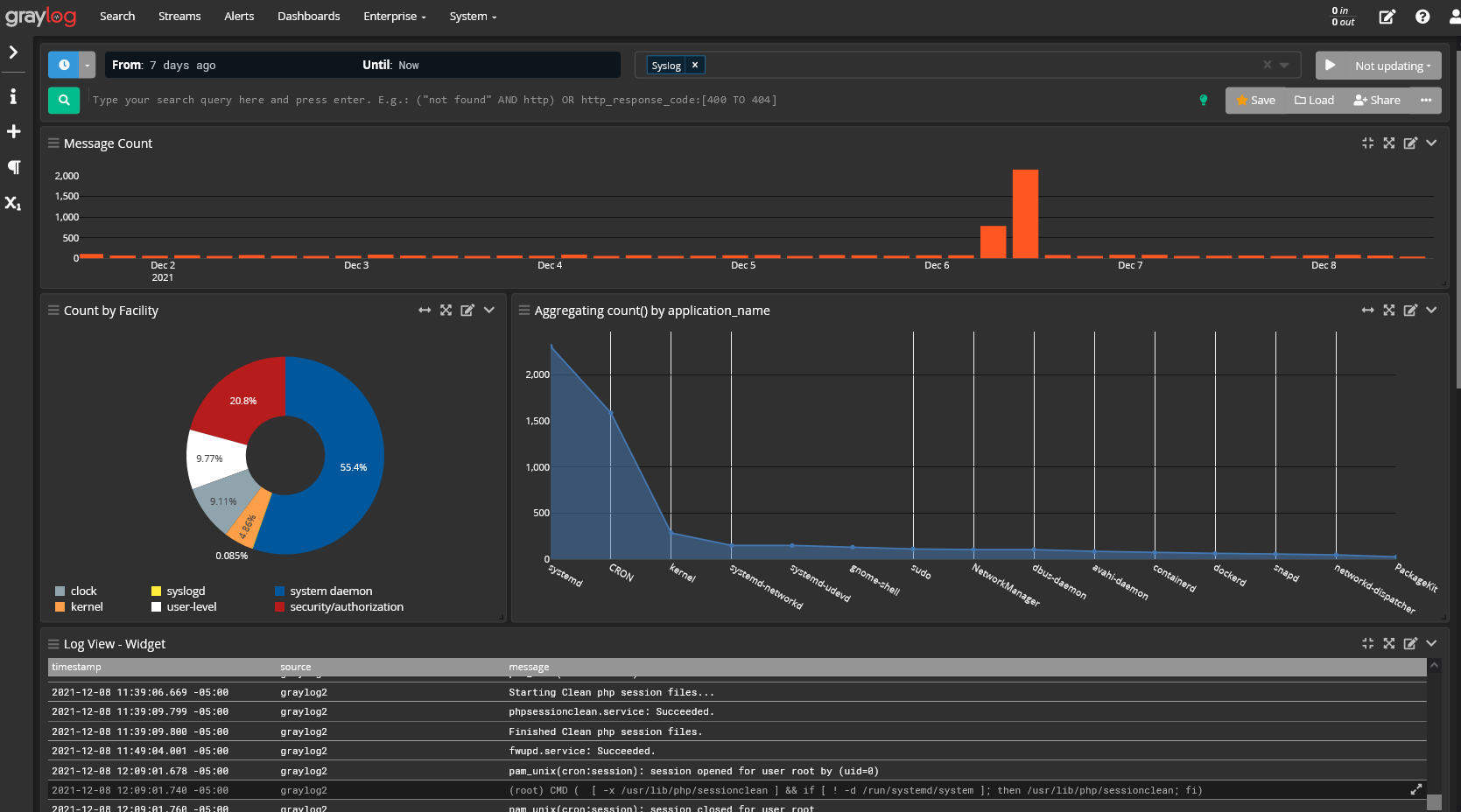
When you’re adding or subtracting fractions, you need to make sure that they have a common denominator, a number that allows you to compare values. In the same way, your
It’s maintenance time! As Graylog has released a new version it’s time to buckle down and get your environment updated. Watch the “5.0 Graylog Upgrade How-to” video. The video also
Follow Us:
© 2024 Graylog, Inc. All rights reserved