
- August 14, 2020
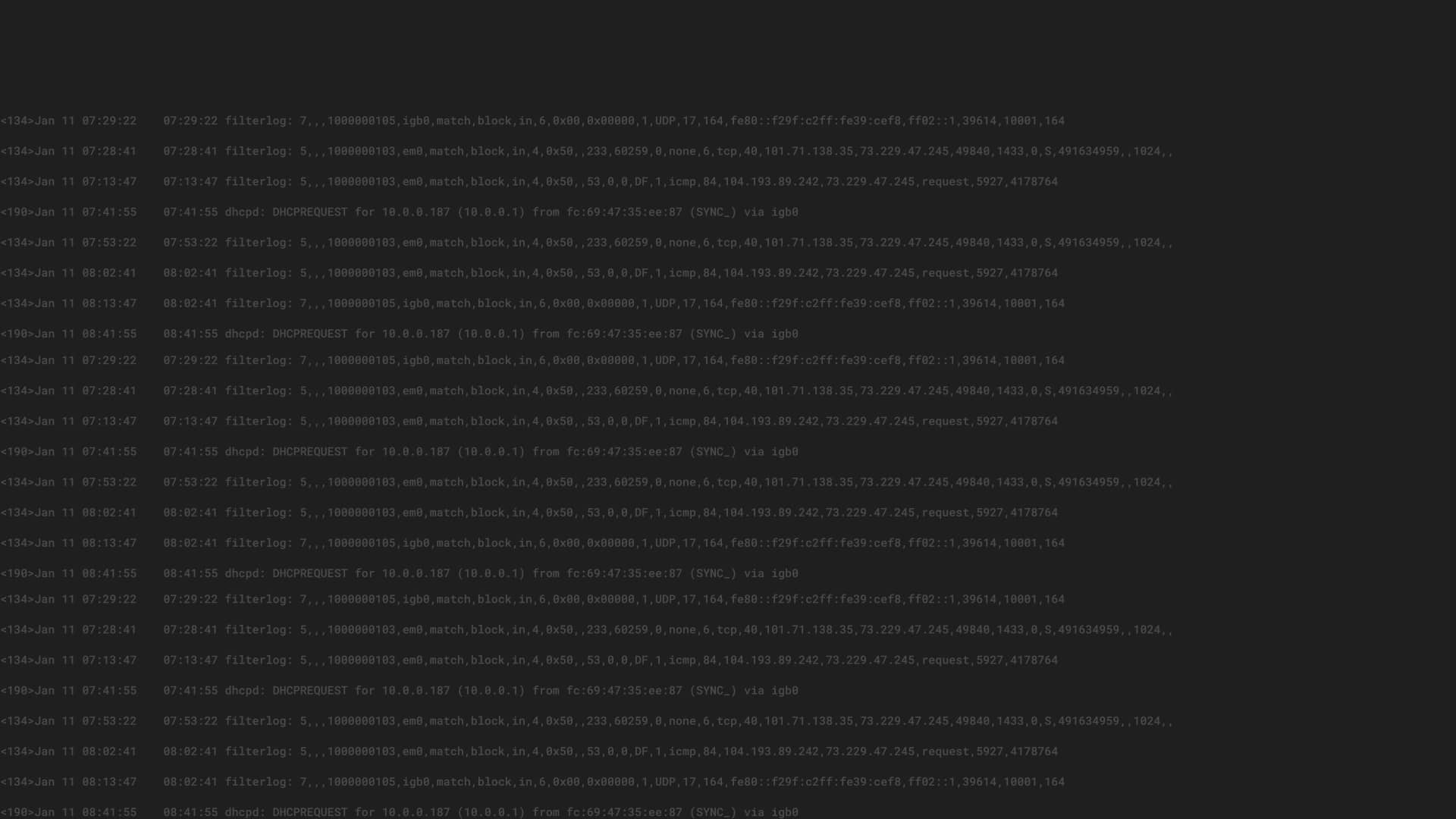
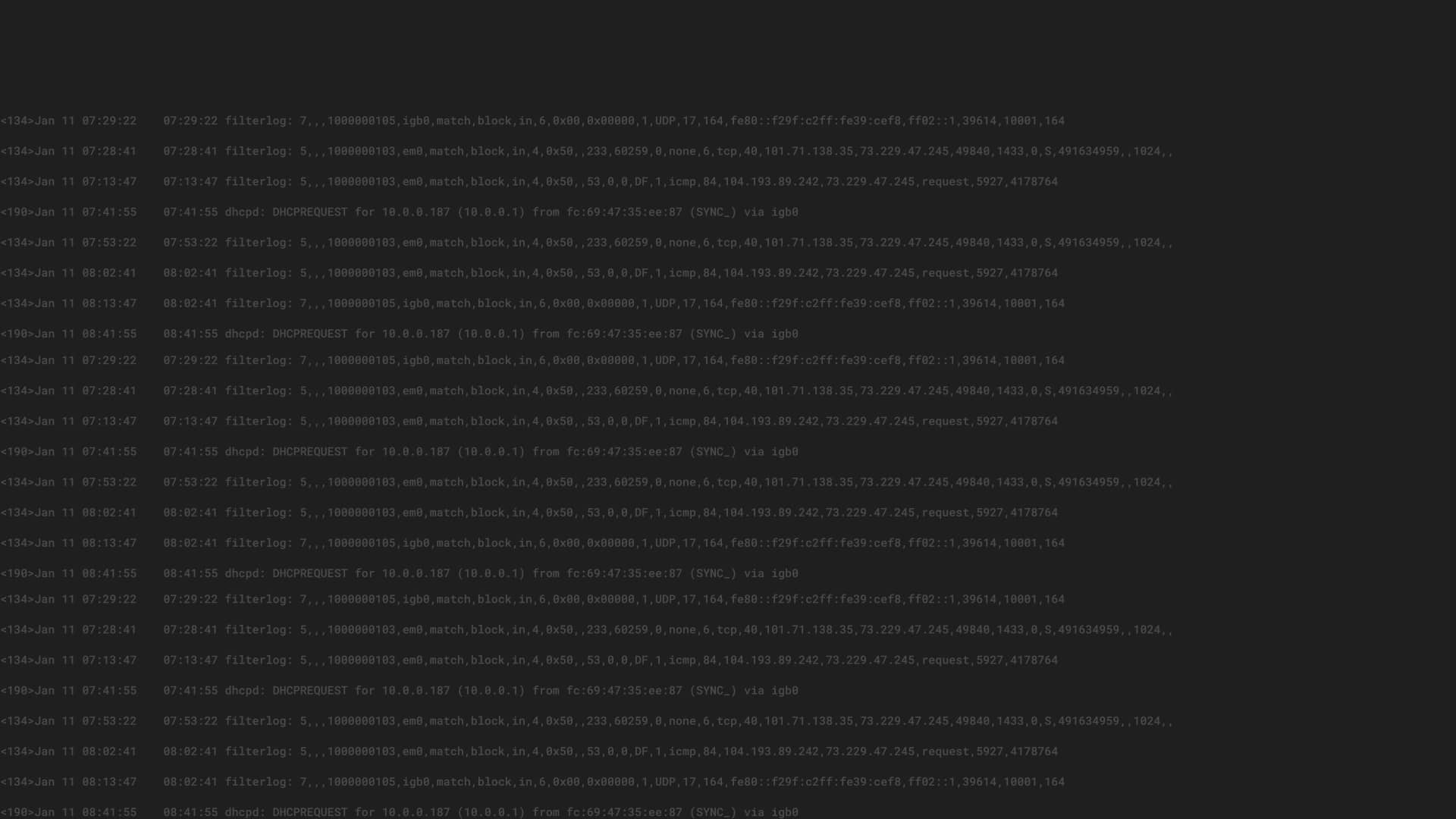
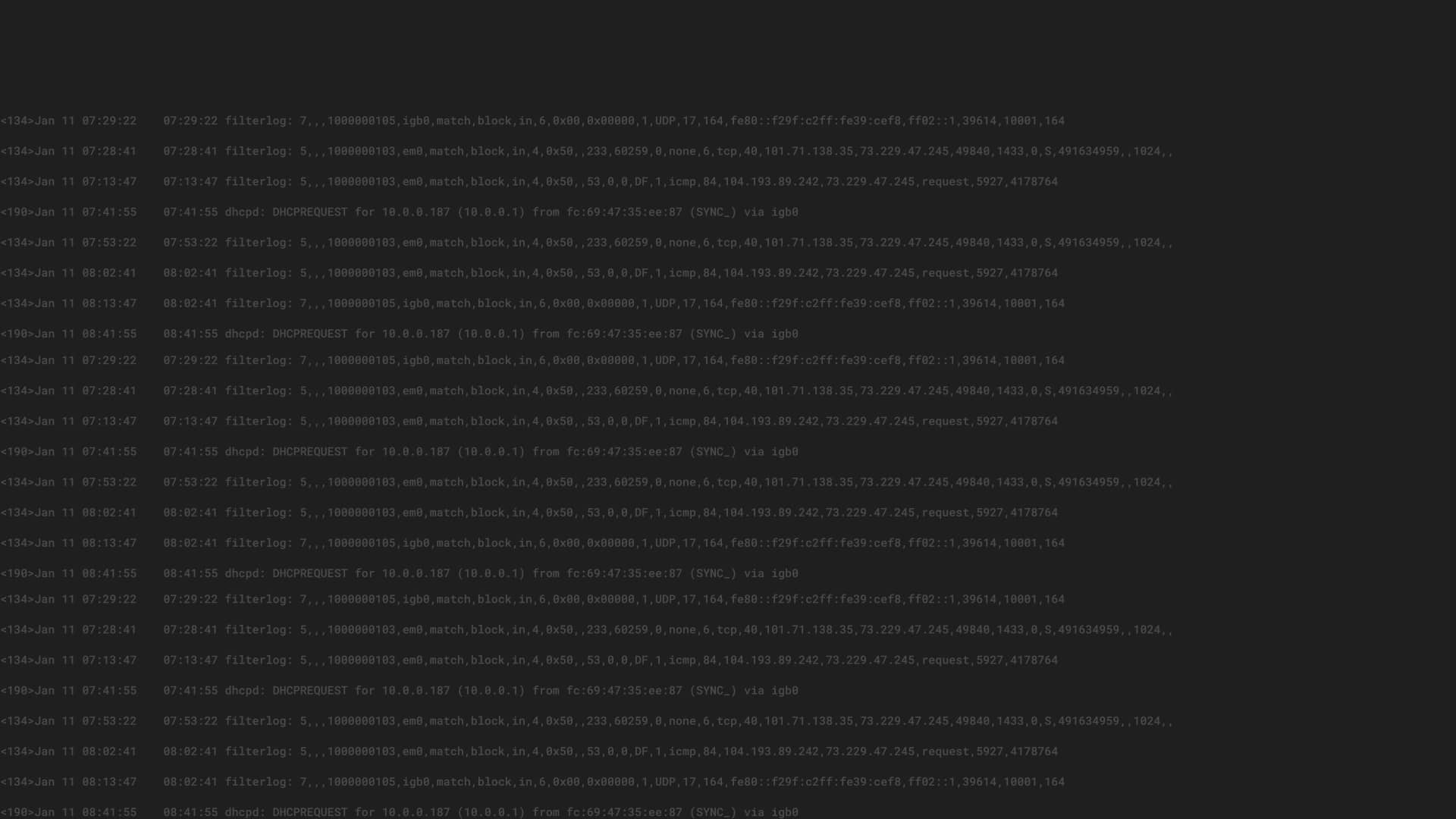
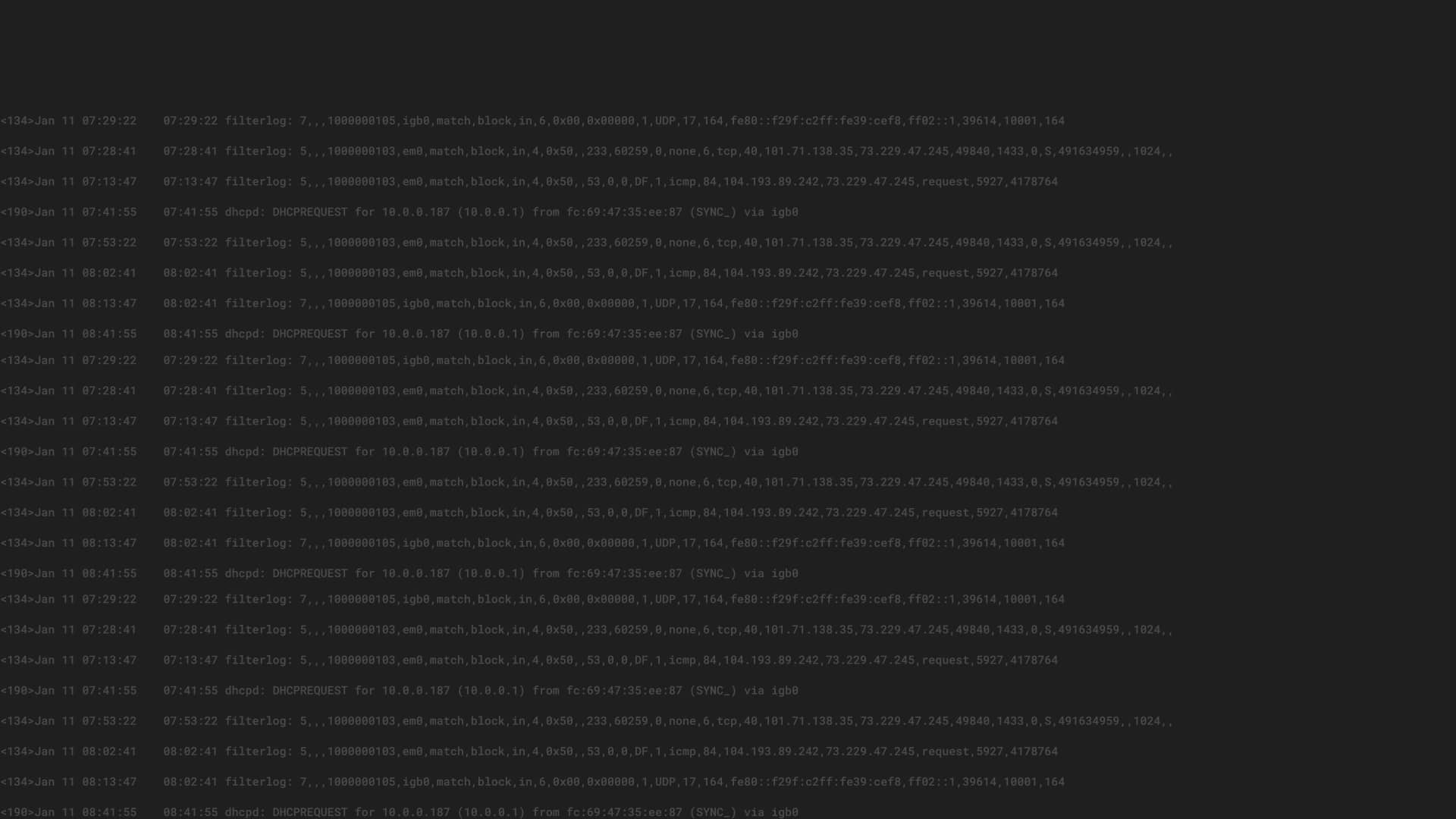
With automated blocking, analysts can focus on higher value activities than responding to obvious security threats that can be safely handled with an automated response.




Follow Us:
© 2024 Graylog, Inc. All rights reserved